Architecture
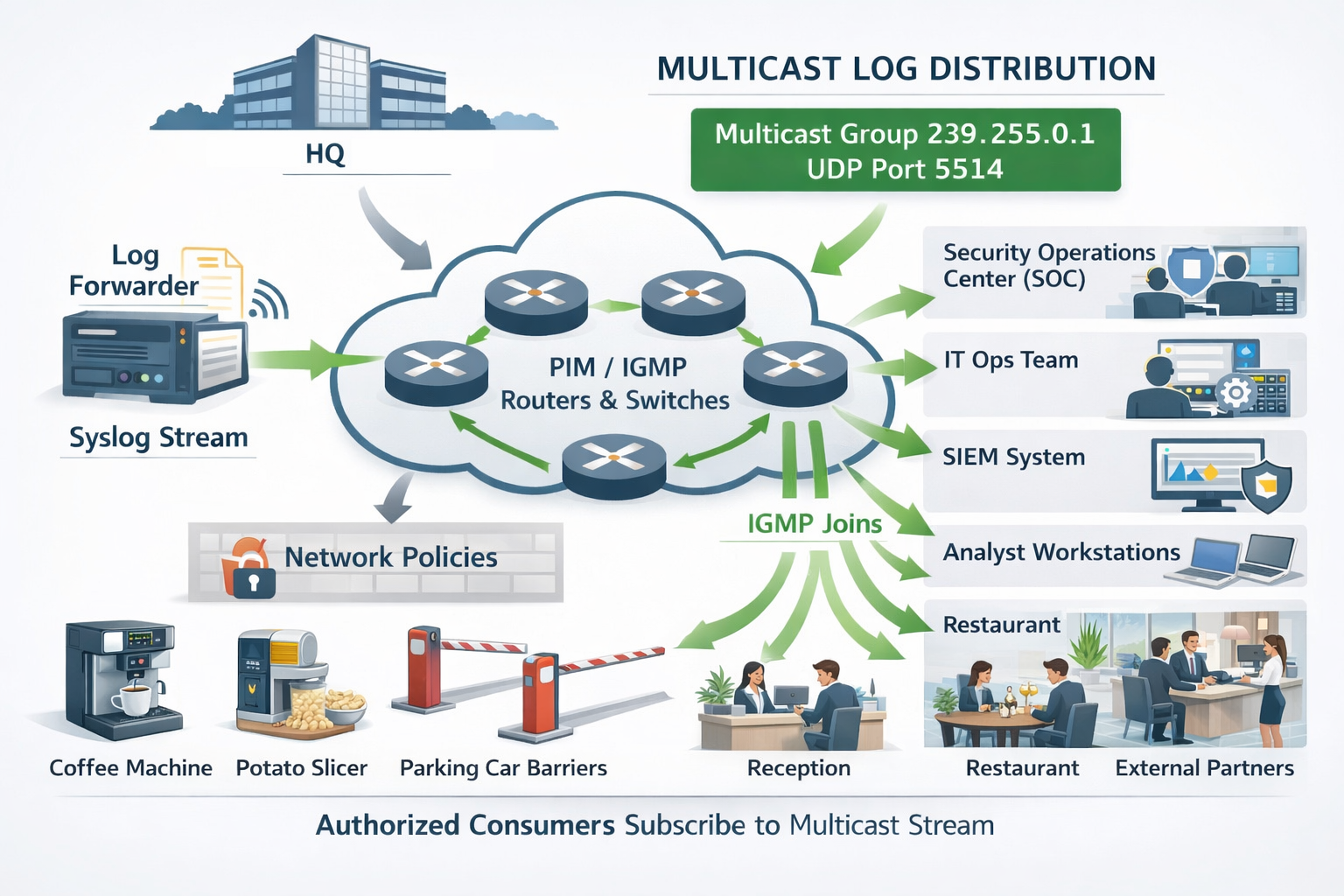
Enterprise-Grade Multicast Log Distribution
One sender. Infinite receivers. Zero extra bandwidth. Welcome to the future that was always hiding in your network stack.
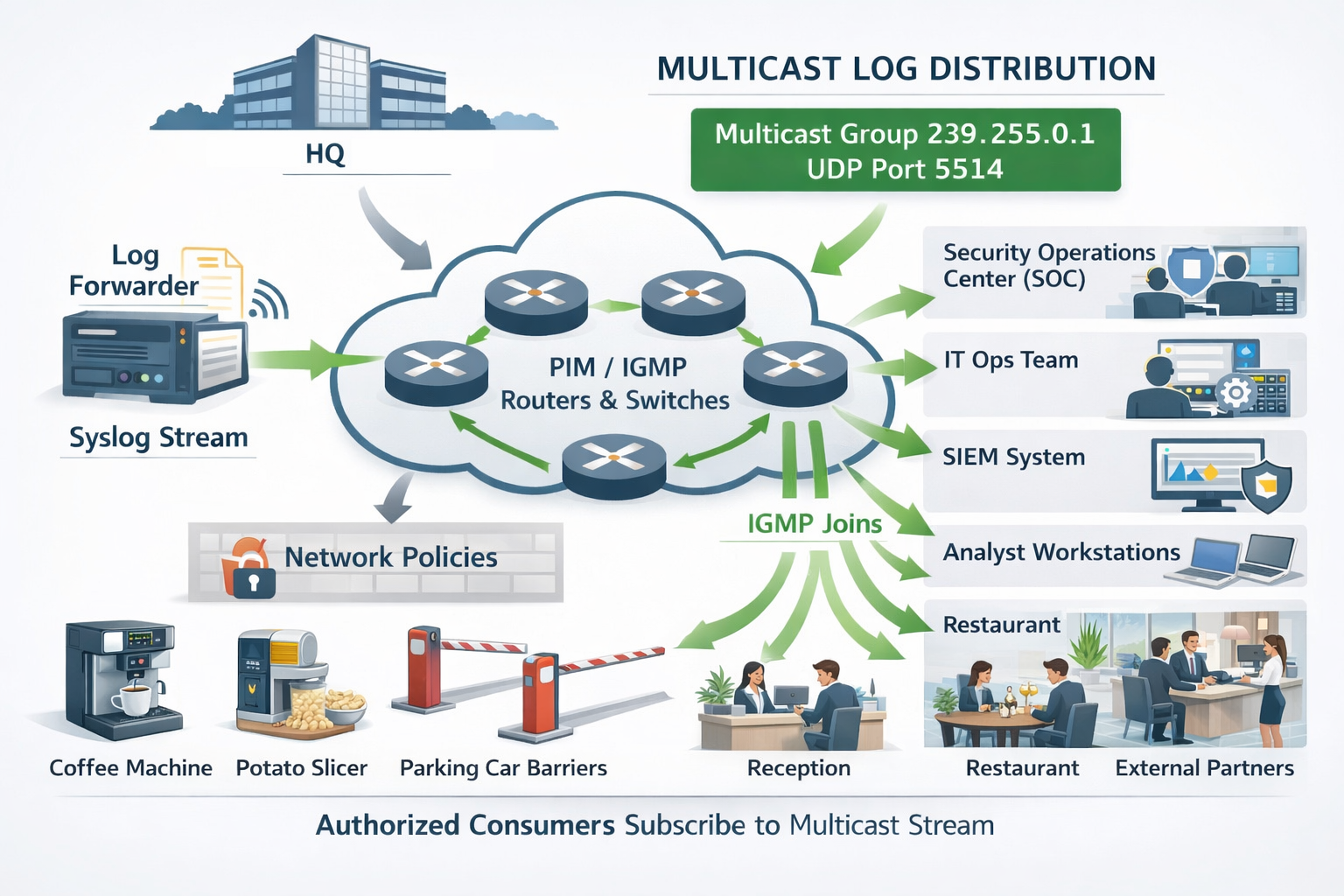
logHiive brings IP multicast to syslog distribution. Send once, receive everywhere. The future of enterprise observability started April 1st, 2026!
Architecture
One sender. Infinite receivers. Zero extra bandwidth. Welcome to the future that was always hiding in your network stack.
Why logHiive
* and by "modern" we mean 1986 RFC 966 multicast
A single multicast stream reaches every consumer simultaneously. Organization-wide observability without N-to-N forwarding nightmares.
Security and ops teams correlate events independently, in real time, without waiting for centralized pipelines to slowly chew through your data.
Each packet is sent exactly once. The network duplicates it where needed. Your bandwidth bill will think you shut down the log pipeline entirely.
Use whatever tool you want: socat, tcpdump, a custom Go binary, or just nc piped into grep like it's 1999. We don't judge.
How It Works
If your network supports IGMP (and it probably does, hiding in shame), you're 90% there.
A single Go binary. Point it at your syslog source and a multicast group. Done. Go get coffee.
Consumers send an IGMP join to 239.255.0.1. Your switches handle the rest. Yes, the switches. They've been waiting for this moment.
Every subscriber gets every log. In real time. Over UDP. What could possibly go wrong?
Quick Start
No YAML. No Helm charts. No 47-page runbook. Just a binary and a dream.
What People Are Saying
* citations pending legal review
Multicast lets us put the right data in front of more eyes without duplicating traffic. It's a force multiplier for both security and reliability.
Our analysts can now correlate events in seconds using the tools they already trust, with zero waiting on centralized pipeline changes.
I just ran socat and suddenly I could see every log in the building. I didn't even ask for permission. Is that... is that okay?
Rollout Plan
Because even chaos needs a schedule.
Network team enables multicast routing. Internal runbooks written. Nobody reads them.
Multicast log distribution goes live network-wide. Your office becomes the first fully multicast-observable building in the country.
Topic-specific groups, TLS unicast mirrors for the paranoid, and metadata enrichment for the ambitious.
Proposal submitted to IETF. Every enterprise replaces Splunk with socat. Stock markets react.
Your logs are already out there. All you have to do is listen.
IGMP Join Now